Dominion Cyber Articles

Search...
Deep Dive into Intrusion Detection Systems (IDS): Signature vs. Anomaly-based Detection.
Key Takeaways: Signature-based IDS: Signature-based intrusion detection systems rely on pre-defined patterns or signatures to identify known threats. These systems are effective in detecting known attacks and are relatively easy to implement. Behavior-based IDS: Behavior-based intrusion detection systems analyze the behavior of network traffic and systems to identify anomalies that may indicate a potential security breach. These systems are better equipped to detect new or unknown attacks. Choosing the right IDS solution: When selecting an intrusion detection system, organizations should consider factors such as their specific security needs, budget, and technical expertise. It is important to evaluate the strengths and limitations of both signature-based and behavior-based IDS and choose a solution that aligns with the organization’s requirements. Introduction Deep

Modern DDoS Attacks: Understanding Multi-vector Strategies and Defense Mechanisms.
Key Takeaways: Modern DDoS attacks are becoming more sophisticated and diverse, utilizing multi-vector strategies to overwhelm target networks and exploit vulnerabilities in various protocols and applications. Application-level attacks, such as targeting popular platforms like WordPress and Joomla, as well as databases, have become common methods for exploiting weaknesses and causing disruption. Zero-day DDoS attacks pose a significant threat, leveraging newly discovered vulnerabilities that have not yet been patched, making them difficult to defend against. Various flooding techniques, such as ping floods, IP null attacks, CharGEN floods, SNMP floods, NTP floods, SSDP floods, and fragmented HTTP floods, are used to overwhelm networks and exhaust resources, amplifying the impact of the attacks. To defend against multi-vector DDoS attacks, organizations must implement robust

Exploring Cyber Threat Landscapes: Region-specific Threats, Actors, and Responses.
Key Takeaway: Understanding region-specific cyber threats is crucial: Different regions face unique cyber threats and challenges. It is important to have a comprehensive understanding of these threats to develop effective cybersecurity strategies. Regional variations in cyber incidents: The EMEA region experiences a high number of cyber incidents, with Germany and the United Kingdom being prominent targets. France exhibits concerns related to malicious employees. In the APAC region, organizations are particularly concerned about nation-states and trusted third-party threats. Regional variations in phishing, malware, and ransomware incidents are also observed. In the Americas, cybercrime is the greatest concern, with worries about cyber terrorists and hacktivists. Mitigating region-specific threats requires tailored approaches: Each region requires specific best practices and recommendations to address its

Physical Security in the Digital World: Safeguarding Data Centers, Offices, and Hardware.
Key Takeaway: Physical security is crucial in the digital world: Safeguarding data centers, offices, and hardware is essential to protect sensitive information from physical threats such as theft, vandalism, and natural disasters. Implementing physical security controls in data centers is vital: Data centers house critical infrastructure and contain valuable data. Utilizing access control systems, surveillance cameras, and intrusion detection systems can help prevent unauthorized access and ensure the security of the data center. Fire protection systems and infrastructure design are key for data center protection: Data centers require robust fire protection systems, including fire suppression systems and fire-resistant construction materials. Proper infrastructure design, including redundant power and cooling systems, is also important to minimize downtime and maintain data center security.

Exploring the Dark Web: Understanding Its Infrastructure, Operations, and Threats.
Key Takeaway: The Dark Web is a hidden part of the internet that requires special software to access. It is used for various purposes, including illegal activities, anonymous communication, and circumvention of censorship. The infrastructure of the Dark Web is based on a network of encrypted servers and routing protocols that help maintain anonymity and privacy. Tor, also known as The Onion Router, is commonly used to access the Dark Web. Operations on the Dark Web involve illicit activities such as drug trafficking, weapon sales, human trafficking, and hacking services. Cryptocurrencies like Bitcoin are often used for transactions to maintain anonymity. The Dark Web poses significant threats, including identity theft, data breaches, malware distribution, and cybercrime. Users must be
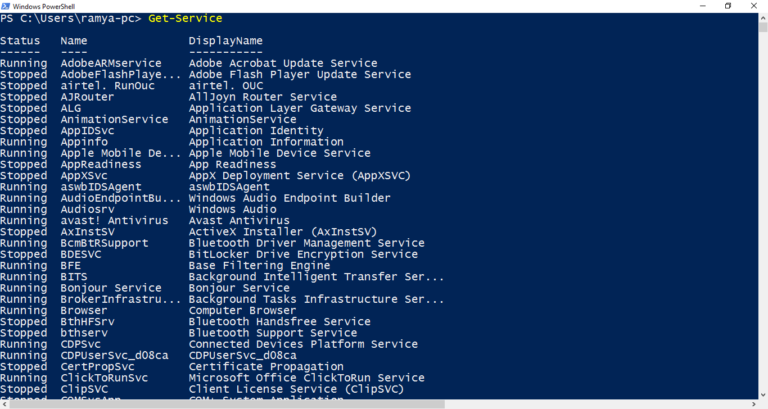
PowerShell for Pentesters: Harnessing Microsoft’s Tool for Advanced Exploitation.
Key Takeaway: PowerShell has become a powerful tool for pentesters, providing advanced exploitation capabilities. Its rise in popularity is driven by its versatility and extensive functionality. PowerShell can be used for various pentesting tasks, including exploiting vulnerabilities in Active Directory. PowerView is a useful tool for gathering user information and detecting weaknesses in AD attributes, which can then be leveraged for social engineering attacks. PowerShell empowers IT security staff by providing an object-oriented shell and powerful coding capabilities. Leveraging PowerShell attributes and ForEach operators allows for efficient and effective scripting, while filtering and output manipulation enhance command execution. In practical examples, PowerShell can be used to hide payloads in text files, execute payloads for exploitation, and mitigate PowerShell-based attacks.

Unmasking Equation Group: Shedding Light on Cybersecurity’s Green Guardians
Introduction While not directly confirmed, this group is widely believed to be affiliated with the U.S. National Security Agency (NSA). They are known for their sophisticated tools and tactics, including the creation of advanced malware and exploitation techniques. Unmasking Equation Group: Shedding Light on Cybersecurity’s Green Guardians The world of cybersecurity is constantly evolving, with new threats and actors emerging every day. Among these, Equation Group has gained considerable attention and intrigue. This article aims to delve into the significance of Equation Group in cybersecurity and shed light on their activities, members, controversies, and implications for the future. Equation Group, often associated with being one of the most sophisticated cyber espionage actors, is a highly skilled and secretive collective of

Unmasking Turla (Snake, Uroburos) The Shadowy World of a State Sponsored Cyber Espionage
Introduction This group is believed to be Russian-sponsored and has been active for several years, targeting embassies, military entities, and research institutions mainly in the Middle East and Europe. Turla, the elusive state-sponsored cyber espionage group, has long been a subject of intrigue and concern in the world of cybersecurity. Known for their sophisticated and stealthy operations, Turla has been involved in targeted attacks against government entities, diplomatic institutions, and industries across the globe. The origins of Turla can be traced back to its early exploits, with a history that spans several years. It has evolved into a formidable threat actor, constantly adapting its methods and techniques to evade detection and maintain their covert operations. The motivations and objectives behind

Unveiling OceanLotus APT32 Investigating Suspected Ties To The Vietnamese Government In Cyber Espionage
Introduction Originating from Vietnam, OceanLotus is believed to be state-sponsored and has targeted foreign companies investing in Vietnam’s manufacturing, consumer products, and hospitality sectors. Cyber espionage is a growing threat in today’s digital world, with governments and other entities targeting sensitive information for various purposes. One prominent actor in the cyber espionage landscape is OceanLotus, also known as APT32. In this article, we delve into the details of OceanLotus, its history, techniques, and suspected ties to the Vietnamese government. To begin, let’s understand what cyber espionage entails. Cyber espionage refers to the covert gathering of information from targeted individuals, organizations, or governments through unauthorized access to computer systems or networks. It involves activities such as data theft, monitoring communications, and

Cyber Sleuths Uncover Charming Kitten Unmasking Iranian Cyber Espionage
Introduction Also believed to be from Iran, this group often uses phishing tactics, targeting political dissidents, human rights activists, and journalists. Key Takeaway: The threat of Charming Kitten: Charming Kitten is a notorious Iranian cyber espionage group known for its sophisticated operations and malicious activities. Understanding and addressing this threat is crucial for cybersecurity professionals and organizations. The origins and operations of Charming Kitten: Charming Kitten’s activities can be traced back to Iran and its state-sponsored cyber warfare initiatives. The group employs various tactics, such as phishing, social engineering, and malware attacks, to compromise targets and steal sensitive information. Notable cyberattacks and operations: Charming Kitten has been involved in high-profile cyberattacks and operations, targeting individuals and organizations in the political,
